Verified Cyber Controls for Canadian Businesses
There is a meaningful difference between having a cyber security control in place and having a verified cyber control. A verified control is one where you have documented evidence — not just a configuration setting — that the control is active, configured correctly, and working as intended.
This distinction matters for cyber insurance underwriting. It matters for client security reviews. It matters when your organization has a cyber incident and needs to demonstrate due diligence. The standard is shifting from “we have controls” to “we can prove our controls work.”
What Makes a Cyber Control Verified
A verified cyber control has three characteristics:
- It is documented — there is a record showing the control exists and is configured as described
- It is current — the documentation reflects the current state, not a configuration from two years ago
- It is evidence-based — the documentation includes actual proof (screenshots, logs, exports, test records) rather than assertions
Most Canadian SMBs have controls that meet the first two criteria inconsistently and rarely meet the third. The controls were set up by an IT provider or internal resource, but systematic documentation and evidence collection was never part of the process.
The Seven Core Verified Controls for Canadian SMBs
1. Verified MFA
Multi-factor authentication verification requires evidence that MFA is enforced — not just enabled — on email, remote access, cloud admin panels, and privileged accounts. An MFA policy configuration export showing enforcement scope and enforcement exceptions is the standard evidence format. This is the highest-priority control for most Canadian cyber insurers.
2. Verified Backup Controls
Backup verification requires completion logs, offsite storage confirmation, immutability settings, and a recent restore test record. It is the control with the largest gap between “we have it” and “we can prove it.” See Backup Verification for full requirements.
3. Verified Endpoint Protection
Endpoint detection and response (EDR) or antivirus coverage verification requires a dashboard export showing deployment across managed endpoints, last update status, and any unprotected devices. Coverage gaps — unmanaged or BYOD devices without protection — must be documented and addressed.
4. Verified Email Security
DMARC, SPF, and DKIM configuration verification requires DNS record exports showing current policy settings. For DMARC, the policy level matters — p=none does not protect against spoofing and most insurers now require p=quarantine or p=reject for full credit. DMARC aggregate reports showing domain usage patterns support the verification.
5. Verified Patching Posture
Patch management verification requires documentation of your patch cadence — how quickly critical patches are applied to servers, workstations, and network devices — with a recent patch status report from your patch management tool. The specific timing varies by insurer but most expect critical patches within 30 days of release.
6. Verified Access Controls
Access control verification includes a privileged account review showing who has administrative access to critical systems, and confirmation that access is tied to current employment status (no orphaned accounts). Regular access reviews — at least annually — documented with sign-off are the standard format.
7. Verified Incident Response Readiness
Incident response verification requires a current, documented IR plan with a last-reviewed date and confirmation that key personnel know their roles. It does not require an elaborate plan — but it does require one that is real, current, and accessible when needed.
How Verified Controls Support Insurance and Client Reviews
For cyber insurance renewals, cyber insurance evidence built from verified controls gives your broker a complete package to submit alongside your application. It reduces underwriting back-and-forth, supports accurate premium placement, and reduces the risk of coverage denial based on unverifiable control claims.
For client security reviews and vendor security questionnaires, verified control evidence allows your team to respond with confidence rather than guesswork. The same evidence package that supports your insurance renewal can be adapted for client-facing use.
See also: Cyber Control Verification | Cyber Insurance Evidence | Ransomware Recovery Readiness
Frequently Asked Questions
What is a verified cyber control?
A verified cyber control is a security control that has been documented with evidence — screenshots, configuration exports, logs, or test records — confirming it is active, correctly configured, and current. It is the difference between asserting that a control is in place and being able to demonstrate it.
Why do cyber insurers require verified controls instead of questionnaire answers?
Because questionnaire answers are self-reported and frequently inaccurate. Post-claim investigations regularly reveal that SMBs had controls that were incomplete, misconfigured, or had gaps. Verified control evidence provides a more accurate picture of actual risk posture, which is what underwriters need to place coverage accurately.
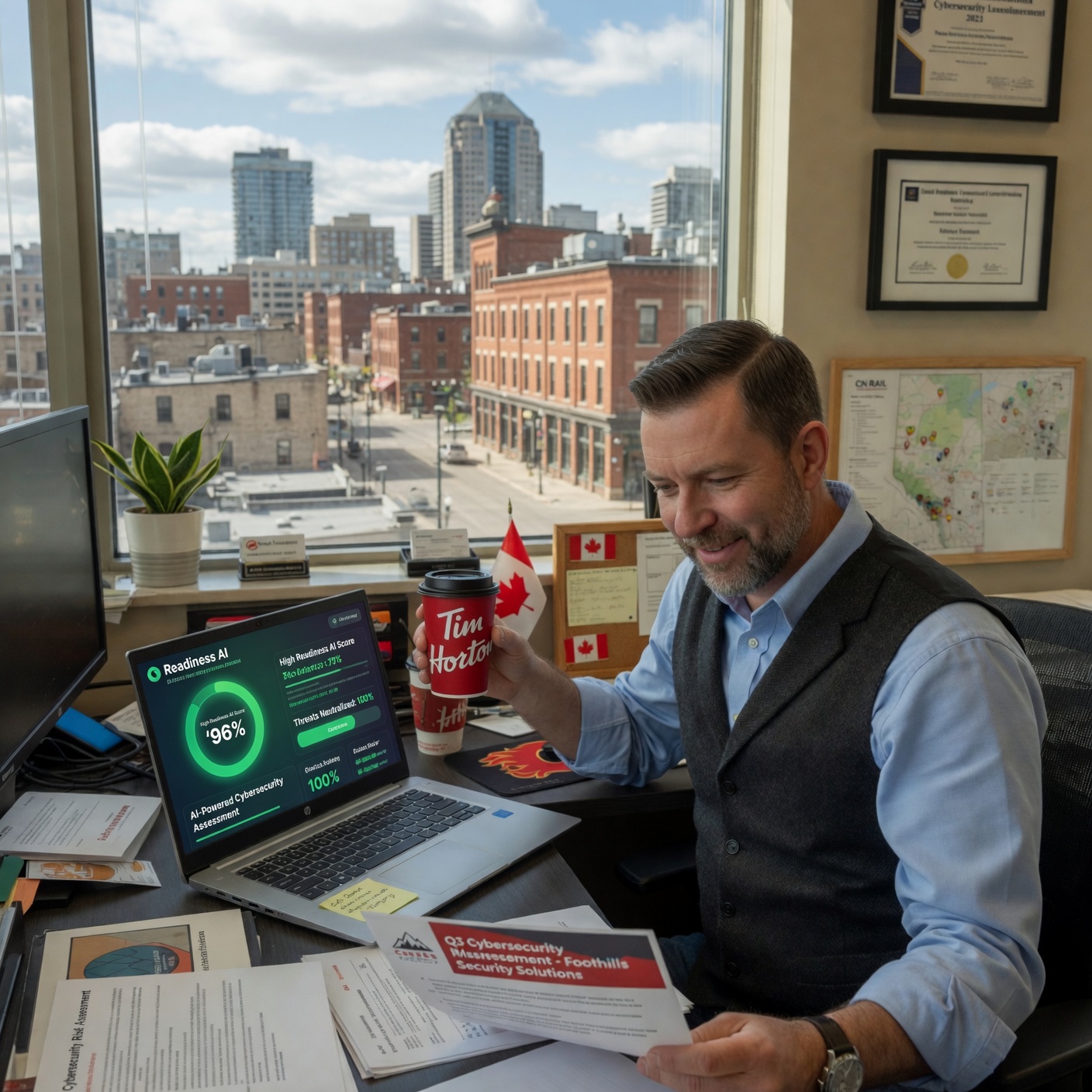
How does Readiness AI help verify cyber controls?
Readiness AI’s verification workflow guides your team through the evidence collection process for each core control. The platform checks evidence against insurer requirements, flags gaps, and generates a packaged evidence bundle for broker or client submission. Start with a Readiness Review to see your current control verification status.
How often do verified controls need to be updated?
Control evidence should be refreshed at least annually — and more frequently for controls where the environment changes often (patching, access controls, endpoint coverage). Most Canadian insurers expect evidence to be current within 12 months for renewal applications. Readiness AI supports ongoing control monitoring so your evidence stays current between renewals.
Ready to verify your cyber controls and build your evidence package? Start a Readiness Review. Related: Cyber Control Verification | Backup Verification | Cyber Insurance Evidence | Private Cyber Verification | Ransomware Recovery Readiness