Ransomware Recovery Readiness for Canadian SMBs
A ransomware incident is not primarily a security event — it is a business continuity event. The organizations that recover in days rather than weeks have one thing in common: they had verified, tested, and documented recovery capabilities before the incident happened.
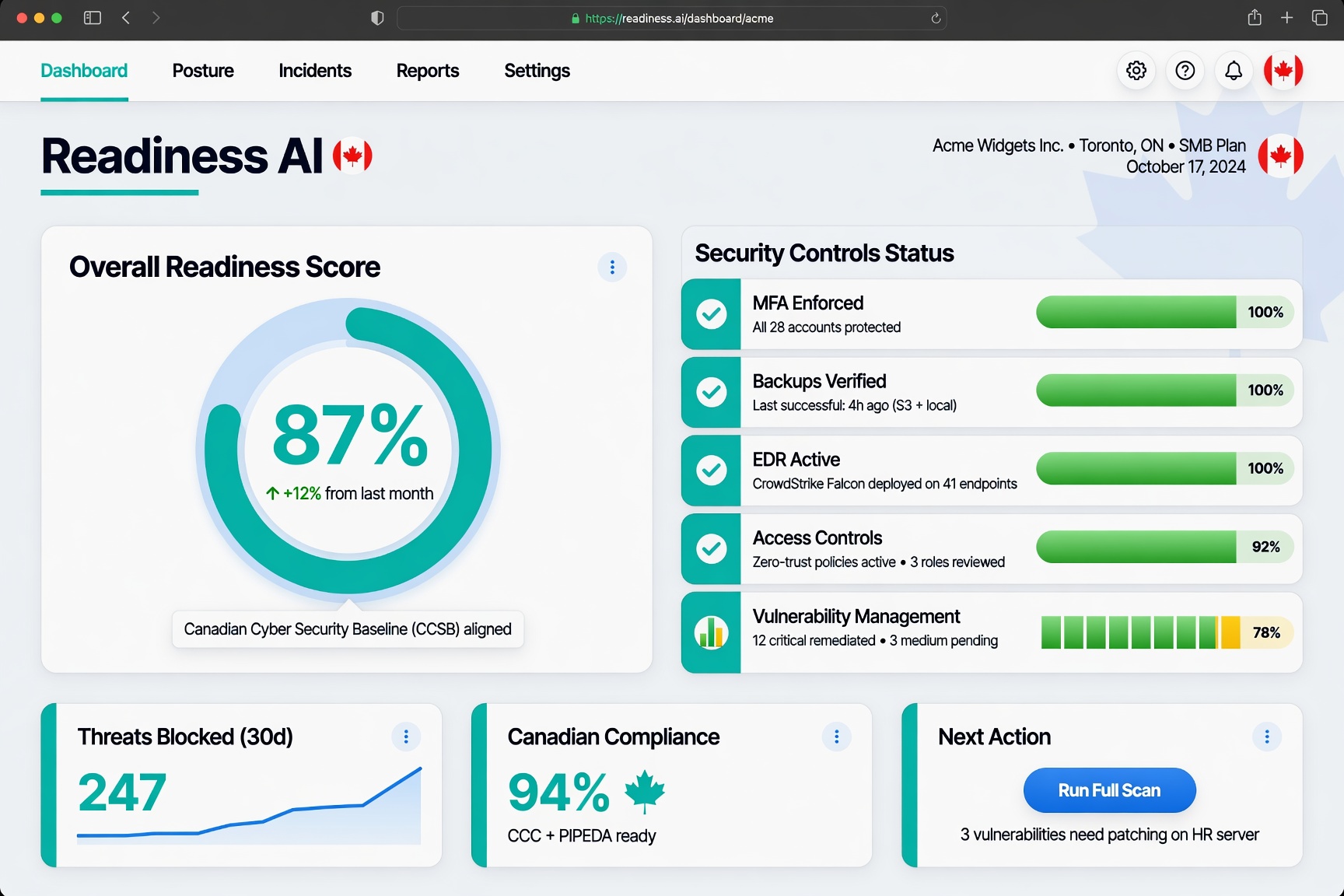
Ransomware recovery readiness is the state of having backup infrastructure, recovery procedures, and incident response documentation in a verified, tested condition. It is measurable and documentable — and Canadian cyber insurers are increasingly asking for that documentation before they write coverage.
Why Recovery Readiness Is the Core Cyber Risk Question
Prevention controls — MFA, EDR, email security, patching — reduce the probability of a successful ransomware attack. They do not eliminate it. For Canadian SMBs, the practical question is not “will we ever be hit?” but “if we are hit, can we recover, and how fast?”
The difference between a business that recovers in 48 hours and one that is down for three weeks is almost entirely a function of backup quality, recovery procedure clarity, and how recently those capabilities were tested. Organizations that had never tested their backups, or had backups connected to production systems that got encrypted, face catastrophic outcomes.
The Components of Ransomware Recovery Readiness
Verified, Immutable Backups
Recovery depends on backups that ransomware cannot encrypt. This requires at least one backup copy stored in an immutable format — object storage with object lock, tape, or air-gapped media — and that backup must be stored separately from production systems on a network segment the ransomware cannot reach.
Backup immutability is now a baseline underwriting requirement for most Canadian cyber insurance carriers. If you cannot demonstrate that your backup storage is immutable, you are unlikely to qualify for coverage at standard rates. See Backup Verification for the full documentation requirements.
Tested Restoration Procedures
Having backups that work theoretically is not the same as having backups that have been tested. Restoration tests reveal problems: corrupted backup files, missing system components, software dependency issues, configuration drift that makes restored systems non-functional without manual remediation.
A restore test should be documented with the date, scope (which systems were tested), and outcome (successful restoration time, issues encountered, remediation actions taken). This record is what insurers ask for, and what separates verifiable recovery readiness from an assumption of readiness.
Defined Recovery Time and Recovery Point Objectives
Recovery time objective (RTO) is how long you can be down before the business impact becomes critical. Recovery point objective (RPO) is how much data loss is acceptable. Both should be defined, documented, and tested. Undefined RTO and RPO mean your organization has never thought through the business impact of an extended outage — a gap that insurers interpret as a readiness risk.
Incident Response Plan
A ransomware-specific incident response plan documents who does what, when, and how during an active incident. It covers initial containment (isolating affected systems), communications (who is notified internally and externally), recovery sequencing (in what order systems are restored), and legal and regulatory obligations (breach notification, insurer notification).
The plan needs to be current and accessible. A plan written in 2020 that doesn’t reflect current systems or personnel has limited value. A plan stored on a system that gets encrypted during a ransomware incident is useless. The plan should be stored offline or in a location accessible independently of your main environment.
Ransomware Recovery Proof for Insurance
When an insurer asks about ransomware recovery capability, they are looking for evidence of the above components — not a general statement that you have a plan. The evidence package for ransomware recovery readiness includes backup verification records, restore test documentation, RTO/RPO definitions, and the incident response plan with its last-reviewed date.
See Cyber Insurance Evidence for how this fits into the broader evidence package insurers require.
Ransomware Recovery for Engineering and Professional Services Firms
Engineering firms, architecture practices, and research organizations face a specific version of the ransomware recovery problem. Their recovery requirements include large file environments (CAD, BIM, simulation data) that take longer to restore than typical office environments. They may have contractual obligations to clients around project continuity. And their backup environments may contain data that cannot be stored in standard cloud recovery platforms.
See Engineering Firm Cyber Readiness and Private Cyber Verification for context on how Readiness AI addresses these firm-specific requirements.
Frequently Asked Questions
What is ransomware recovery readiness?
Ransomware recovery readiness is the documented, tested state of having backup infrastructure, recovery procedures, and incident response plans verified and ready to activate. It is the difference between believing you can recover from a ransomware incident and being able to demonstrate — with evidence — that you can.
What evidence do cyber insurers want to see about ransomware recovery?
Canadian cyber insurers typically ask for backup verification records (completion logs, offsite storage confirmation, immutability settings), restore test documentation (date, scope, and outcome), defined RTO/RPO, and an incident response plan with a current review date. Readiness AI generates evidence packages that cover each of these components.
How often should ransomware recovery capabilities be tested?
Most Canadian cyber insurers expect restore tests to be documented at least annually. Organizations with higher risk profiles — professional services, engineering, regulated businesses — benefit from quarterly testing, particularly for critical systems. The key is that test results are documented, not just that testing occurs.
What is the most common ransomware recovery failure point for Canadian SMBs?
The most common failure point is backup systems that were connected to the primary network environment and got encrypted alongside production systems. The second most common is backups that were running but had never been restore-tested, revealing corruption or missing components at the worst possible moment.
Can Readiness AI help document ransomware recovery readiness?
Yes. Readiness AI’s verification workflow covers backup verification, restore test documentation, RTO/RPO definition, and incident response readiness. The output is an evidence package formatted for insurer review. Start with a Readiness Review to identify your current recovery readiness gaps.
Verify and document your ransomware recovery readiness. Start a Readiness Review. Related: Backup Verification | Cyber Insurance Evidence | Verified Cyber Controls | Engineering Firm Cyber Readiness | Cyber Control Verification