Cyber Insurance Evidence for Canadian SMBs
The shift from self-attestation to documented evidence is the defining change in Canadian cyber insurance underwriting over the past three years. Answering “yes” to questionnaire questions is no longer enough. Insurers want proof — and for many SMBs, producing that proof is the bottleneck between them and affordable coverage.
Cyber insurance evidence is the documented record of your security controls that an insurer or broker can review to assess your actual risk posture. It is the output of a verification process, not a self-declaration.
Why Insurers Are Asking for Evidence
The cyber insurance market in Canada has tightened significantly. Claim frequency and severity in the SMB segment has increased, and insurers responded by requiring more rigorous underwriting data. The result is a gap between what most SMBs can produce and what insurers actually want to see.
The fundamental problem is that self-attestation is unreliable. An SMB that genuinely believes its backups are working may not have tested restoration in two years. An organization that checks “MFA enabled” may have MFA active on email but not on remote access or cloud admin panels. Insurers have seen enough post-claim investigations to know these gaps exist, and they are building evidence requirements into the application process to surface them before a claim.
What Cyber Insurance Evidence Actually Looks Like
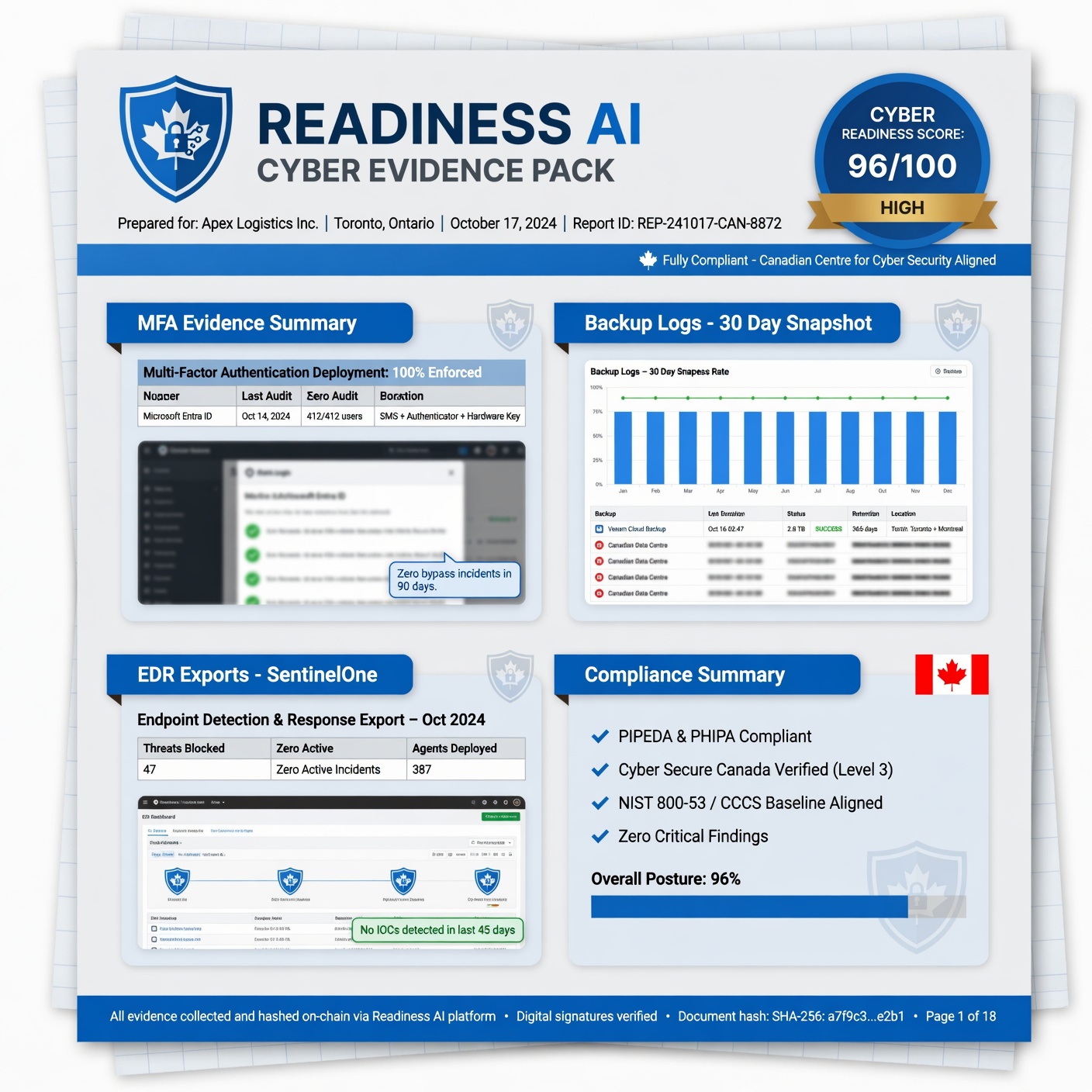
For each core control, an insurer-ready evidence package contains specific documentation — not a general statement that a control is in place.
MFA Evidence
Insurers want to see that MFA is enforced — not just enabled. Evidence includes screenshots or configuration exports showing MFA enforcement policies on email (Microsoft 365 or Google Workspace), remote access (VPN, RDP), cloud admin panels, and any privileged access. An MFA policy document that shows enforcement is applied globally, with documented exceptions, is the standard format.
Backup Evidence
Backup evidence includes recent backup completion logs, confirmation of offsite or cloud storage, immutability settings, and a restore test record. The restore test record is the most commonly missing component. See Backup Verification for a full breakdown.
Endpoint Protection Evidence
EDR or AV deployment evidence shows the platform in use, coverage across managed endpoints, and recent update status. A dashboard export showing deployment coverage and last update date is the standard format.
Email Security Evidence
DMARC, SPF, and DKIM configuration records with enforcement status. A DMARC policy at p=reject or p=quarantine with a DMARC aggregate report showing domain usage is the standard. SPF and DKIM records should be documented alongside the DMARC policy.
Incident Response Evidence
A documented incident response plan with a last-reviewed date and confirmation that key personnel are aware of it. The plan does not need to be elaborate — it needs to exist and be current.
The Evidence Gap Most Canadian SMBs Have
Most Canadian SMBs have controls in place. Most cannot produce the evidence package described above without significant effort. The controls exist — they were set up by an IT provider or an internal resource — but the documentation of those controls, in the format insurers want, was never created.
This is what creates friction at renewal: not the controls themselves, but the inability to demonstrate them in a structured, documented way. Readiness AI is built to close this gap. The verification workflow prompts your team to collect each evidence component, checks it against insurer requirements, and packages it in a format brokers and underwriters can review.
Evidence for Client Security Reviews
Cyber insurance is not the only context where evidence matters. Enterprise clients, government contracting authorities, and professional services clients are increasingly asking their vendors and subcontractors to demonstrate cyber controls. The vendor security questionnaire process — which has become common in Canadian professional services — requires the same evidence package that insurers ask for.
For Canadian SMBs that face both insurance renewals and client security reviews, building an evidence package once and using it across both contexts is the most efficient approach.
Frequently Asked Questions
What is cyber insurance evidence?
Cyber insurance evidence is documented proof that your organization’s security controls are in place, configured correctly, and working. It is the output of a verification process — screenshots, configuration exports, logs, test records — rather than a self-declaration that controls exist.
Why do Canadian insurers want evidence instead of questionnaire answers?
Self-attestation has proven unreliable. Post-claim investigations regularly reveal that SMBs believed their controls were in place but had gaps — backups that weren’t restore-tested, MFA that wasn’t enforced on all systems, email security configured to monitor but not enforce. Insurers are requiring evidence to surface these gaps before a claim, not after.
What format should cyber insurance evidence be in?
Evidence should be organized by control category, with each piece of evidence labelled, dated, and linked to the specific control it documents. Screenshots should include date stamps. Configuration exports should be current. Restore test records should include the date, scope, and outcome of the test. Readiness AI generates evidence packages in this format automatically.
How does Readiness AI generate cyber insurance evidence?
Readiness AI guides your team through a structured verification workflow for each control. The platform prompts evidence collection, checks completeness against insurer requirements, and generates a packaged evidence bundle that your broker can submit alongside your renewal application. Start with a Readiness Review to assess your current evidence gaps.
Can the same evidence be used for both insurance and client security reviews?
Yes. The control evidence format Readiness AI produces is compatible with both cyber insurance underwriting and vendor security questionnaire responses. Canadian SMBs facing both insurance renewals and client security requirements can maintain one evidence package and use it across both contexts.
For a complete list of the security controls Canadian insurers now require, see Cyber Insurance Controls in Canada: What Insurers Require.
Ready to build your cyber insurance evidence package? Start a Readiness Review. Related: Verified Cyber Controls | Backup Verification | Cyber Control Verification | Ransomware Recovery Readiness | Sample Evidence Pack