
Cyber Insurance Controls in Canada: What Insurers Require in 2026
Cyber insurance controls Canada insurers expect have become stricter in recent years. If you want to qualify for coverage, avoid exclusions, and keep premiums reasonable, you need to show evidence that key security controls are actually in place. In Alberta and across Canada, the controls most often tied to cyber insurance readiness align closely with practical guidance from CyberAlberta, the NIST Cybersecurity Framework 2.0, and CIS Critical Security Controls v8.
Core Cyber Insurance Controls Required in Canada
Yes. Cyber insurance is available to Canadian businesses of all sizes — from sole proprietors to enterprises. There is no legal barrier to obtaining coverage. The question is not whether you can buy a policy, but whether an insurer will offer you one at a reasonable price, with adequate limits, and without significant exclusions.
Why Canadian Insurers Require Proof of Security Controls
Canadian cyber insurers have significantly tightened their underwriting criteria since 2020. A business insurers evaluating cyber insurance controls vewould have been approved with a basic application five years ago may now receive a decline, a sub-standard offer, or a co-insurance requirement if it cannot demonstrate specific security controls. The controls that most affect your eligibility are not exotic — but they must genuinely be in place.
Common Control Gaps That Lead to Denied Coverage
Canadian cyber insurers apply a standard set of underwriting criteria. The following controls are now considered baseline requirements by most carriers operating in the Canadian market. Missing one or more of these is the most common reason applications are declined or coverage is restricted.
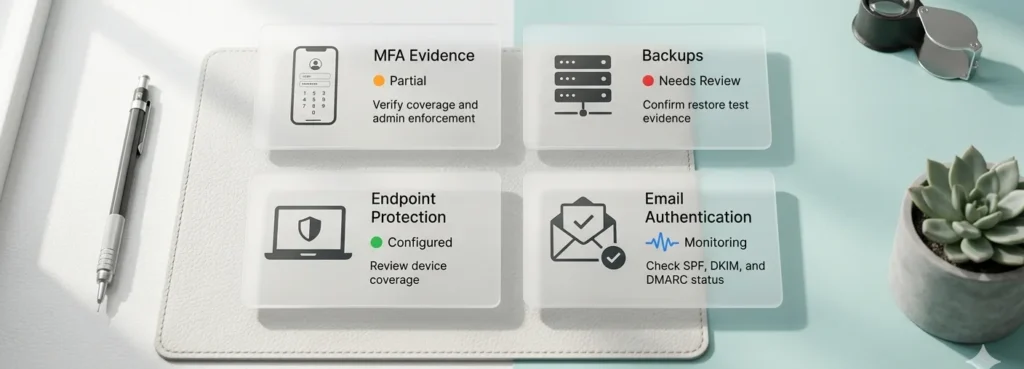
Multi-factor authentication (MFA)
MFA is the single most important control for cyber insurance eligibility in Canada. Insurers require MFA on email accounts, remote access tools (VPN, RDP), cloud services, and privileged or administrative accounts. A business that cannot confirm MFA deployment across these systems is considered high-risk by most underwriters and will face limited coverage options or outright declines.
Tested, offline backups
Insurers want evidence of offline or immutable backups stored separately from your primary network. A backup that is connected to your environment can be encrypted in a ransomware attack — and insurers are well aware of this. You should be able to confirm how frequently backups run, how long restoration takes, and when the backups were last tested. Untested backups are treated with the same skepticism as no backups at all.
Endpoint detection and response (EDR)
Basic antivirus software is no longer sufficient for cyber insurance purposes. Most Canadian insurers now require endpoint detection and response (EDR) tools that provide real-time threat detection and can contain incidents automatically. EDR is expected across all workstations, servers, and any device that accesses your corporate environment.
Incident response planning
Underwriters ask whether your business has a documented incident response plan — a written procedure for what happens when a breach occurs. The plan does not need to be lengthy or complex, but it must exist, be accessible to the right people, and identify roles and escalation paths. Organizations that can produce a current, tested plan are viewed as materially lower risk than those that cannot.
Employee security awareness training
Phishing is still the leading initial attack vector in Canada, and insurers want to see evidence that employees have received security awareness training within the last 12 months. Some underwriters also ask about the frequency of phishing simulations. Training does not need to be expensive or time-consuming — it just needs to be documented and completed.
Privileged access management
Insurers increasingly ask about how administrative and privileged access is managed. This means limiting who has domain admin or root access, ensuring those accounts use separate credentials from standard user accounts, and maintaining a log of who has access to what. Unrestricted privileged access is a significant red flag in a cyber insurance application.
Patch management
Operating systems, applications, and network devices must be kept current with security patches. Insurers want to know whether you have a defined patch cadence and whether critical patches are applied within a defined window. Organizations running end-of-life operating systems (such as Windows Server 2012 or older) may face coverage restrictions.
How does the Cyber Insurance Controls Application Process Work?
A cyber insurance application is a detailed questionnaire. You will be asked to confirm whether each of the above controls is in place — and to describe how they are implemented. Applications are largely self-reported, but insurers have become increasingly diligent about verifying answers, particularly at renewal or after a claim.
Misrepresentation on a cyber insurance application — even unintentional — can result in a denied claim. The most defensible position is one where your application answers are backed by documented evidence: security assessments, configuration records, training logs, and backup test results that confirm your controls are genuinely implemented.
What if I don’t have all the Cyber Insurance Controls in Place?
You can still apply for cyber insurance with gaps in your controls — but you should expect that to be reflected in your coverage terms. Common outcomes for businesses with incomplete controls include higher premiums, lower policy limits, ransomware sub-limits or co-insurance requirements, or explicit exclusions for certain attack types.
The practical path forward is to identify your gaps before you apply, remediate where possible, and accurately report your current posture. Brokers who specialize in cyber insurance can advise on which gaps are dealbreakers and which can be mitigated through other means — but they need accurate information to do that effectively.
What is the fastest way to prepare a strong application?
The fastest way to prepare a strong cyber insurance application is to conduct a cyber risk assessment before you apply. An assessment gives you a documented baseline of your current controls, identifies gaps, and produces evidence you can include with your submission. This changes your application from a set of self-reported checkboxes to a verified record of what is actually in place.
Readiness AI generates a verified security evidence report specifically designed for cyber insurance applications and renewals. You can complete the assessment, receive your report, and share it with your broker — all before your next application deadline.How to Validate Your Cyber Insurance Controls
See your security posture before your next renewal
Readiness AI generates a verified security evidence report you can share with your broker or include with your next cyber insurance application or renewal.
Start AssessmentFrequently Asked Questions About Cyber Insurance Controls in Canada
Can a small business get cyber insurance in Canada?
Yes. Cyber insurance is available to small businesses in Canada, including businesses with fewer than 10 employees. Premiums for small businesses with good security hygiene are often lower than owners expect. The same core controls apply — MFA, tested backups, endpoint protection — but the depth of implementation expected scales with business size and complexity.
What is the minimum cyber insurance requirement for most insurers?
Most Canadian insurers treat MFA on email and remote access, tested backups, and EDR endpoint protection as their non-negotiable baseline. A business that cannot confirm all three in place will have very limited options in the current market. Everything beyond that — incident response plans, privileged access management, training — affects pricing and policy terms rather than eligibility outright.
Will my existing IT provider confirm my controls for the insurer?
Some IT providers will provide letters or documentation supporting your insurance application. However, insurer-provided questionnaires ask about specific technical controls in specific terms, and not all IT providers are familiar with what underwriters are actually looking for. An independent security assessment gives you documentation that is specifically formatted for this purpose and is not subject to provider bias.
I was declined for cyber insurance — what should I do?
A decline is almost always related to specific missing controls — most commonly MFA, backup quality, or endpoint protection. Start by requesting the specific reasons for the decline from your broker. Address the identified gaps, then reapply with documentation that demonstrates the remediated controls. A security assessment before reapplication gives you the clearest picture of where you stand and what evidence to include.
Does my industry affect whether I can get cyber insurance?
Yes. High-risk sectors — including healthcare, legal, financial services, and critical infrastructure — face more rigorous underwriting scrutiny and typically pay higher premiums. Businesses in these sectors may also face lower policy limits or more restrictive exclusions. Strong security controls are even more important in these industries, because the baseline expectations are higher and the consequences of a breach are more severe under Canadian privacy law.
How does my security posture affect my cyber insurance premium?
Insurers use your security controls to price risk. A business with strong, documented controls — MFA across all systems, immutable backups, EDR, a tested incident response plan, and current security training — will typically pay significantly less per dollar of coverage than a business with partial controls. In some cases, the difference in premium between a well-documented and a poorly-documented application for the same business can be 30 to 50 percent. Documented evidence of controls changes how underwriters assess and price your application.
Specific cyber insurance controls such as MFA, EDR, tested backups, and incident response planning are now baseline requirements for most Canadian carriers.
Implementing the right cyber insurance controls before renewal can significantly reduce premiums and prevent coverage gaps.
A pre-renewal assessment of cyber insurance controls provides documented proof that satisfies underwriter requirements.