Logistics and operations businesses — including freight carriers, trucking companies, 3PLs, warehousing operations, customs brokers, and supply chain providers — are increasingly asked to demonstrate cyber readiness by shippers, partners, customers, and insurers. The operational nature of these businesses doesn’t reduce the cyber exposure. It often amplifies it.
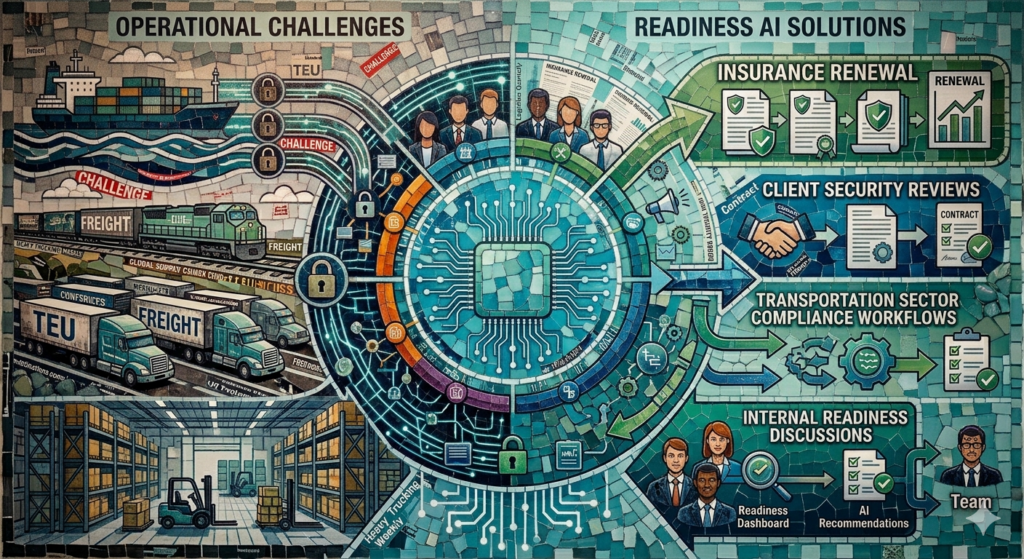
Readiness AI helps logistics and operations businesses organize cyber control evidence for insurance renewal, client and partner security reviews, transportation sector compliance workflows, and internal readiness discussions.
Why this matters
Supply chain attacks have made every link in the logistics chain a target. A ransomware attack that takes down dispatch software, electronic logging devices (ELDs), or warehouse management systems can halt operations within hours — creating immediate financial loss and cascading liability to shippers and clients who depend on delivery commitments.
Large shippers and retail clients are now embedding cyber requirements into carrier and 3PL contracts. Customs brokers face specific requirements related to CBSA data security. And cyber insurance underwriters have significantly tightened coverage for logistics businesses after a wave of ransomware claims targeting TMS, ELD, and dispatch systems. Being asked for cyber evidence is no longer unusual in this sector — it’s becoming standard practice.
What you’re asked to prove
Logistics and operations businesses are typically asked to provide evidence in four situations:
- Cyber insurance underwriting and policy renewals
- Shipper or enterprise client security questionnaires during contract onboarding or renewal
- Carrier compliance reviews from freight brokers or load boards
- CBSA or cross-border partner security assessments for customs broker operations
Stakeholders want to see proof that your business:
- Enforces multi-factor authentication for all staff accessing TMS, dispatch, and customer portals
- Maintains encrypted, tested backups of operational data, customer shipment records, and financial systems
- Patches and updates all office workstations and any internet-connected operational systems
- Provides security awareness training to office and dispatch staff
- Controls and logs access to shipper data, customer records, and financial systems
- Has documented policies for access provisioning and deprovisioning for drivers and contractors
- Uses email authentication to prevent domain spoofing and freight fraud
- Has a documented incident response and operational continuity plan for cyber events
Common blind spots
TMS and dispatch software with no MFA: Transportation management systems and dispatch platforms are often configured without multi-factor authentication — either because it’s not the default setting or because operational staff push back on the friction. Insurers specifically ask about MFA on operational systems, and the answer is frequently “no” for logistics businesses.
Driver and contractor access never deprovisioned: Drivers, contractors, and seasonal staff frequently receive access to portals, mobile apps, and dispatch systems that is never formally revoked when they leave. User access review is one of the most common gaps found during readiness reviews in the logistics sector.
Freight fraud and email spoofing: The logistics sector is a primary target for fraud involving spoofed carrier emails, fake load confirmations, and redirected wire transfers. Strong email authentication (SPF, DKIM, DMARC) is one of the most important controls for logistics businesses — and one of the most frequently missing or misconfigured.
Operational systems treated as IT-exempt: Many logistics operators draw a distinction between “office IT” and “operational systems” like GPS tracking, ELDs, and warehouse management platforms. Insurers and enterprise clients don’t draw that line. Any system connected to the internet, storing business data, or accessed by staff is in scope for a security review.
No business continuity plan for a cyber event: Most logistics businesses have operational continuity plans for equipment failures or weather events, but no documented plan for what happens when their TMS or dispatch software is taken offline by ransomware. Insurers ask specifically about cyber-specific continuity planning, and the absence of documentation creates coverage risk.
What Readiness AI helps organize
Readiness AI helps organize the practical evidence behind cyber readiness. That can include evidence summaries, screenshots, exports, configuration records, policy references, access review notes, backup records, email authentication records, and readiness notes. This gives logistics and operations businesses a clear, organized response when an insurer, shipper, or enterprise client asks for documented control evidence.
- MFA and access control evidence
- Endpoint protection evidence
- Backup and recovery evidence
- Email authentication evidence
- Patch posture evidence
- User access review notes
- Security policy references
- Incident response readiness notes
Readiness AI provides similar cyber readiness evidence solutions for other industries. Learn more on our Industries page or read more Articles about cyber readiness evidence.
Frequently asked questions
We’re a trucking company, not a tech company. Why do we need cyber readiness evidence?
Because shippers, brokers, and insurers are asking. Modern logistics operations run on connected software — TMS, ELDs, GPS tracking, online portals, email. A ransomware attack that takes down your dispatch system for three days creates real operational and financial loss. Insurers want to know your controls are in place before they cover that risk. Clients want to know before they trust you with their cargo.
Our IT is managed by an outside provider. Do we still need to provide evidence?
Yes. Your managed IT provider implements controls — but you are accountable for demonstrating that those controls are working. When an insurer or shipper asks for evidence, your IT provider’s service agreement isn’t a substitute for documented control evidence. Readiness AI helps gather and organize that evidence, often working from records your IT provider already has.
How is Readiness AI different from a cybersecurity consultant?
Cybersecurity consultants typically assess and remediate technical security gaps. Readiness AI focuses specifically on organizing the evidence that proves your controls are working — the documentation layer that insurers, clients, and auditors actually ask to see. The two are complementary: your IT or security provider implements controls; Readiness AI helps you document and organize the evidence of those controls.
Prepare your operation before the insurer or shipper asks
Readiness AI helps logistics and operations businesses organize cyber readiness evidence before insurance renewal, a client security review, or a freight partner questionnaire becomes urgent.
Readiness AI helps organize cyber readiness evidence. It does not provide legal advice, insurance advice, privacy advice, breach response, certification, or a guarantee of insurance approval, regulatory compliance, claim acceptance, or breach prevention. Logistics and operations businesses should consult qualified legal, insurance, and security advisors for advice specific to their situation.