Technology companies — including SaaS providers, IT service firms, managed service providers, software developers, and digital agencies — face a unique challenge when it comes to cyber readiness. They are often the most technically sophisticated businesses in a client’s vendor ecosystem, yet they face intense scrutiny precisely because of the level of access they hold to client systems, data, and infrastructure.
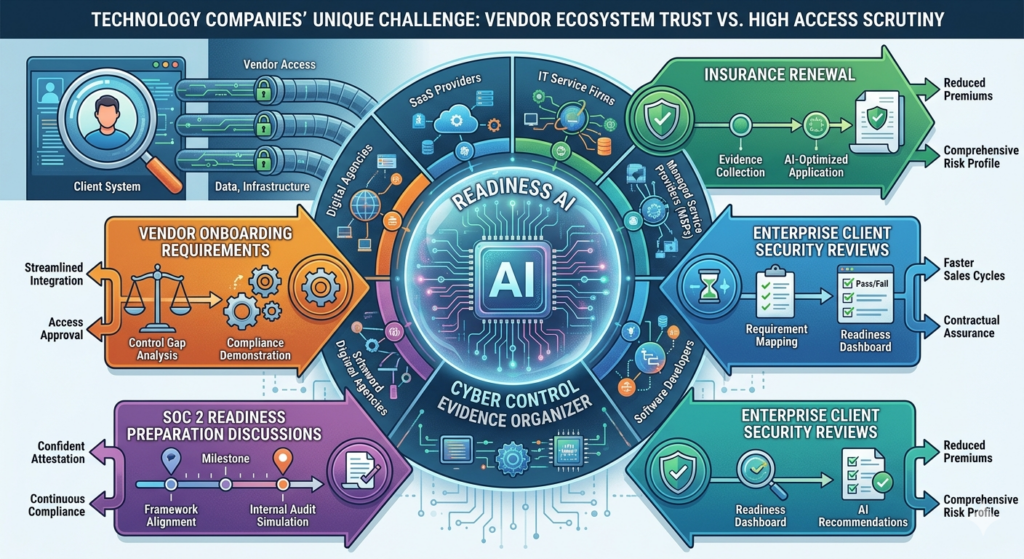
Readiness AI helps technology companies organize cyber control evidence for insurance renewal, enterprise client security reviews, vendor onboarding requirements, and SOC 2 readiness preparation discussions.
Why this matters
Enterprise procurement teams have significantly tightened their vendor security requirements. Technology vendors accessing client data, networks, or systems are routinely asked to complete security questionnaires — and increasingly, questionnaire answers alone are not sufficient. Clients want to see evidence: configuration exports, policy documents, audit logs, and control summaries that verify controls are actually in place.
Cyber insurance underwriters view technology companies as higher-risk insured parties because a single breach can cascade to dozens or hundreds of downstream clients. Premium increases, coverage restrictions, and underwriting denials are common for technology firms that cannot demonstrate robust control evidence. And with PIPEDA obligations and growing data residency expectations in Canada, the compliance pressure is increasing alongside the commercial pressure.
Many technology companies also face the irony of being assumed to have strong security because of what they do — while actually operating with the same gaps as any other SMB. Being a software company doesn’t automatically mean your internal controls are documented and evidenced.
What you’re asked to prove
Technology companies are typically asked to provide evidence in four situations:
- Enterprise client vendor security questionnaires during procurement or contract renewal
- Cyber insurance underwriting and policy renewals
- SOC 2 readiness discussions or pre-audit gap assessments
- Partner and reseller channel security onboarding requirements
Stakeholders want to see proof that your company:
- Enforces multi-factor authentication and privileged access management for all staff, especially those with production system access
- Maintains encrypted, tested backups of code repositories, databases, and client data
- Applies security patches rapidly to operating systems, frameworks, libraries, and dependencies
- Provides security awareness training and has a documented secure development lifecycle
- Enforces role-based access control and logs access to production environments and client data
- Separates production and development environments with appropriate access restrictions
- Uses email authentication and endpoint protection across the entire team
- Has a documented incident response plan and breach notification process
Common blind spots
Production access without formal controls: Many small technology companies allow developers to access production environments directly without formal change management, access logging, or privileged access controls. This is one of the first things enterprise security teams look for — and one of the most common gaps found in readiness reviews.
Dependency and open-source library vulnerabilities: Modern software projects rely on hundreds of open-source libraries. Knowing which dependencies have known vulnerabilities — and having a documented process for addressing them — is a specific control that enterprise clients and insurers are increasingly asking about.
Developer laptops as the weakest link: Developers often have local copies of production data, database credentials stored in local config files, and SSH keys that grant direct production access — all on laptops with inconsistent patch levels and no MDM enrollment. This creates a significant uncontrolled access path that is difficult to explain to an underwriter.
Shared cloud credentials and service accounts: Technology companies frequently use shared IAM credentials, API keys, or service account passwords across team members. Shared credentials cannot be traced to individuals, cannot be selectively revoked, and are a material control failure from an insurance and client security standpoint.
No documented data handling for client data in dev/test: Production data used in development or testing environments is a common privacy and security gap. Enterprise clients ask specifically whether their data appears in non-production systems, and many technology companies don’t have a clear documented answer.
What Readiness AI helps organize
Readiness AI helps organize the practical evidence behind cyber readiness. That can include evidence summaries, screenshots, exports, configuration records, policy references, access review notes, backup records, email authentication records, and readiness notes. This gives technology companies a clear, organized response when an enterprise client security team, insurer, or procurement auditor asks for documented control evidence.
- MFA and access control evidence
- Endpoint protection evidence
- Backup and recovery evidence
- Email authentication evidence
- Patch posture evidence
- User access review notes
- Security policy references
- Incident response readiness notes
Readiness AI provides similar cyber readiness evidence solutions for other industries. Learn more on our Industries page or read more Articles about cyber readiness evidence.
Frequently asked questions
We’re a small software company. Do enterprise clients really audit us?
Yes — especially if you have access to their systems or data. Enterprise procurement teams have standardized vendor security review processes that apply to all vendors, regardless of size. Being small doesn’t exempt you; it often means you face more scrutiny because you’re assumed to have fewer controls.
Is Readiness AI a SOC 2 audit preparation service?
No. Readiness AI helps technology companies organize practical cyber control evidence — the kind of documentation that is useful for insurance renewals, client security questionnaires, and internal readiness discussions. Many of the controls involved overlap with SOC 2 Trust Service Criteria, but Readiness AI is not an audit firm and does not produce SOC 2 reports.
We already have security tools. Do we still need Readiness AI?
Having security tools and being able to prove those tools are configured and working are two different things. Many technology companies have strong technical controls but have never organized the documentation that demonstrates those controls to external reviewers. Readiness AI helps bridge that gap.
Prepare your company before the enterprise security review arrives
Readiness AI helps technology companies organize cyber readiness evidence before a client questionnaire, insurance renewal, or procurement audit turns into a deal-blocking gap.
Readiness AI helps organize cyber readiness evidence. It does not provide legal advice, insurance advice, privacy advice, breach response, certification, or a guarantee of insurance approval, regulatory compliance, claim acceptance, or breach prevention. Technology companies should consult qualified legal, privacy, insurance, and security advisors for advice specific to their situation.