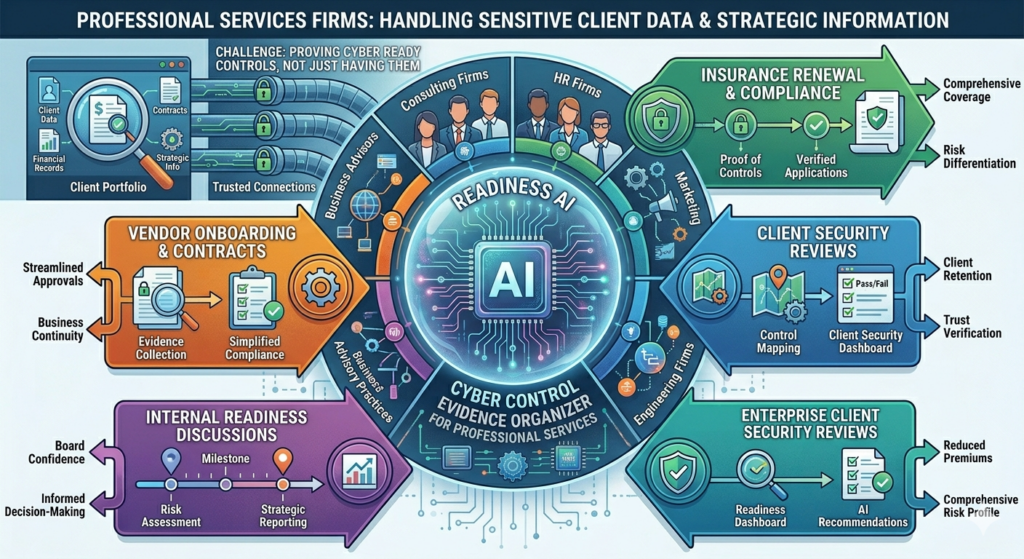
Professional services firms — including consultants, HR firms, marketing agencies, engineering firms, and business advisory practices — handle sensitive client data, contracts, financial records, and strategic information on behalf of their clients. When an insurer, client, procurement team, or internal leader asks about cyber readiness, the challenge is rarely whether you have controls in place. The challenge is whether you can prove it.
Readiness AI helps professional services firms organize cyber control evidence for insurance renewal, client security reviews, vendor onboarding, and internal readiness discussions.
Why this matters
Professional services firms are increasingly targeted by cyber attackers because they hold access to client systems, sensitive business strategies, and financial data — often with less security infrastructure than the enterprises they serve. Clients, especially enterprise and public sector clients, are tightening their vendor security requirements and routinely asking professional services providers to complete security questionnaires, provide insurance certificates, or demonstrate control evidence before renewing contracts.
Beyond client pressure, cyber insurance underwriters have significantly raised their standards for professional services firms. Simply answering “yes” to questionnaire items about MFA or backups is no longer enough. Underwriters want to see documentation that controls actually work.
What you’re asked to prove
Professional services firms are typically asked to provide evidence in four situations:
- Client security reviews and vendor onboarding questionnaires before contract award or renewal
- Cyber insurance underwriting and policy renewals
- Internal risk reviews or board-level security discussions
- Procurement requirements from enterprise or government clients
Stakeholders want to see proof that your firm:
- Enforces multi-factor authentication for all staff accessing client systems and firm data
- Maintains encrypted, tested backups of client deliverables and engagement files
- Tracks software patches and security updates across all workstations and remote devices
- Provides security awareness training to all employees and contractors
- Controls and logs access to client data and project systems
- Has documented data handling, retention, and disposal policies
- Reviews vendor and subcontractor security before granting access to client information
- Has a documented incident response plan for data breaches or ransomware events
Common blind spots
Client data scattered across platforms: Professional services teams often work across email, shared drives, project management tools, and collaboration platforms simultaneously. Without a clear data map, it’s difficult to prove where client data lives, who can access it, and how it’s protected.
Subcontractors and freelancers with live access: Many firms engage independent contractors who are granted access to client systems during an engagement and never fully deprovisioned afterward. This creates access control gaps that are difficult to explain during a client security review.
No formal security awareness program: Phishing is the most common entry point for professional services firm breaches. Without documented training records, it’s hard to demonstrate that staff know how to identify and respond to social engineering attempts.
Verbal security commitments, no written evidence: Many firms verbally assure clients that “we take security seriously” but have never documented their controls, policies, or evidence. When a client formally requests proof, the gap becomes apparent.
No incident response plan: A data breach affecting client information is a business-ending event for a professional services firm if handled poorly. The absence of a documented response plan turns a manageable incident into a crisis that damages client trust permanently.
What Readiness AI helps organize
Readiness AI helps organize the practical evidence behind cyber readiness. That can include evidence summaries, screenshots, exports, configuration records, policy references, access review notes, backup records, email authentication records, and readiness notes. This gives professional services firms a clear, organized response when a client, insurer, or procurement team asks for proof that basic controls are in place.
- MFA and access control evidence
- Endpoint protection evidence
- Backup and recovery evidence
- Email authentication evidence
- Patch posture evidence
- User access review notes
- Security policy references
- Incident response readiness notes
Readiness AI provides similar cyber readiness evidence solutions for other industries. Learn more on our Industries page or read more Articles about cyber readiness evidence.
Frequently asked questions
My clients haven’t asked for security documentation yet. Do I still need this?
Enterprise and government clients are increasingly embedding security review requirements into standard vendor onboarding and contract renewal workflows. Building your evidence now means you’re ready to respond quickly when the request arrives — rather than scrambling to assemble documentation under a contract deadline.
What if I use Microsoft 365 or Google Workspace — doesn’t that handle security?
Cloud platforms provide security infrastructure, but you’re still responsible for how your team uses those platforms. MFA enforcement, access controls, data retention settings, and admin privilege reviews are all your responsibility. Readiness AI helps you document that those settings are actually configured and working — not just that you have the platform.
Can the same evidence package be used for multiple client security reviews?
Yes. One set of organized, up-to-date evidence can be tailored to respond to multiple client questionnaires, insurance underwriters, and procurement requirements. Readiness AI organizes evidence by control category so you can quickly generate the specific proof each stakeholder requires.
How quickly can we get organized if a client asks for evidence urgently?
Start with a readiness review. Qualified firms are onboarded to the Readiness AI platform, which helps organize existing control evidence quickly. The goal is to have your evidence ready before the urgent request arrives — not to build it under pressure.
Prepare your firm before the client security review request arrives
Readiness AI helps professional services firms organize cyber readiness evidence before a client questionnaire, insurance renewal, or procurement review turns into a rushed documentation project.
Readiness AI helps organize cyber readiness evidence. It does not provide legal advice, insurance advice, privacy advice, breach response, certification, or a guarantee of insurance approval, regulatory compliance, claim acceptance, or breach prevention. Professional services firms should consult qualified legal, privacy, insurance, and professional advisors for advice specific to their situation.